
Ars Technica: "Last week, security researchers revealed a vulnerability in WiFi Protected Setup, an optional device configuration protocol for wireless access points. WPS lets users enter a personal identification number that is hard-coded into the access point in order to quickly connect a computer or other wireless device to the network. The structure of the WPS PIN number and a flaw in the protocol's response to invalid requests make attacking WPS relatively simple compared to cracking a WiFi Protected Access (WPA or WPA2) password. On December 28, Craig Heffner of Tactical Network Solutions released an open-source version of an attack tool, named Reaver, that exploits the vulnerability.
To find out just how big the hole was, I downloaded and compiled Reaver for a bit of New Years geek fun. As it turns out, it's a pretty big one—even with WPS allegedly turned off on a target router, I was able to get it to cough up the SSID and password. The only way to block the attack was to turn on Media Access Control (MAC) address filtering to block unwanted hardware."

Save a ton of money - and storage - thanks to this 1TB SSD deal that marks the start of Amazon's latest Gaming Week promotion.

The ASUS ProArt Display PA32KCX is on the way - a brand-new 8K monitor designed for professionals, including DisplayPort 2.1 connectivity.
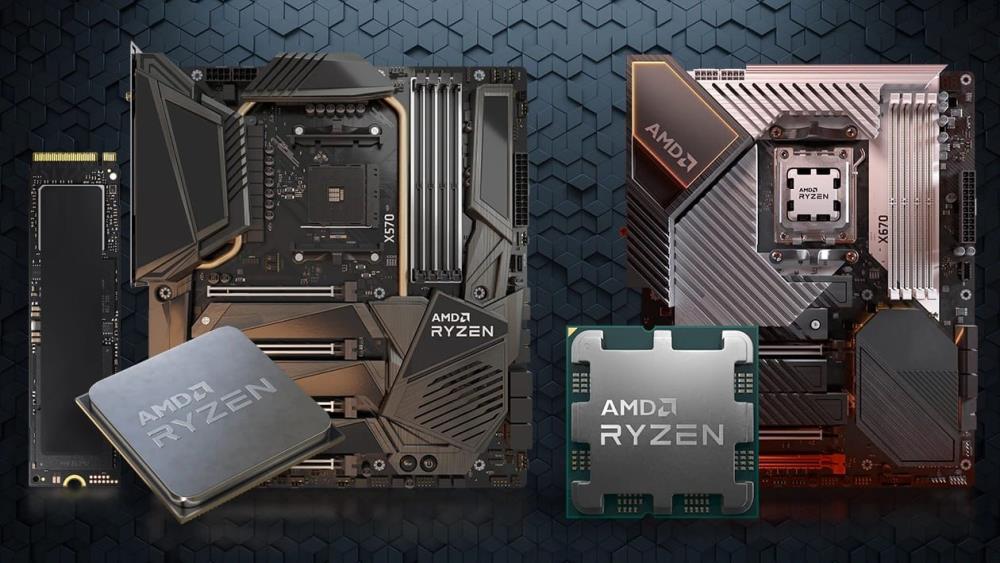
It's time to give your setup the upgrade of its lifetime with this Cyber Monday AMD Ryzen 7 5700X Cyber Monday deal.